Ok, I know nowadays people are begin to switch from Backtrack to Kali Linux, here I just wanna share a new tricks before you start using it. After that, you might wanna run an update and upgrade.
Let's start with open up a new Terminal, go to "/etc/apt/sources.list" you can use any text editor you like gedit, nano, vi or vim. I'm using nano my personal favorite.
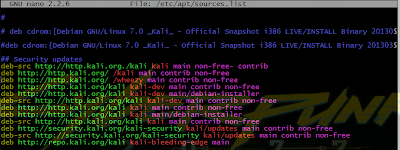 |
| Edit the source.list file before running update and upgrade |
Here are the list of that you need to add to :
deb http://http.kali.org/ /kali main contrib non-free
deb http://http.kali.org/ /wheezy main contrib non-free
deb http://http.kali.org/kali kali-dev main contrib non-free
deb http://http.kali.org/kali kali-dev main/debian-installer
deb-src http://http.kali.org/kali kali-dev main contrib non-free
deb http://http.kali.org/kali kali main contrib non-free
deb http://http.kali.org/kali kali main/debian-installer
deb-src http://http.kali.org/kali kali main contrib non-free
deb http://security.kali.org/kali-security kali/updates main contrib non-free
deb-src http://security.kali.org/kali-security kali/updates main contrib non-free
deb http://repo.kali.org/kali kali-bleeding-edge main
After you had done insert all those, save and quit. And now, you can run update and upgrade to your Kali Linux.
Then start launching msfconsole and see how the different!
 |
| Metasploit before update and upgrade |
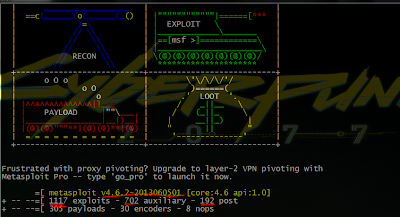 |
| Metasploit after update and upgrade |
It might take times to complete the update and upgrade but it's depends on your internet connection speed. This took me for 1 hour 45 minute (roughly) to complete the downloading and installing the updates to be completed.
That's all for now! May the source be with you!
Credits to : Metasploit News and Tutorials
Comments
Post a Comment